audit2rbac takes a Kubernetes audit log and username as input, and generates RBAC role and binding objects that cover all the API requests made by that user.
-
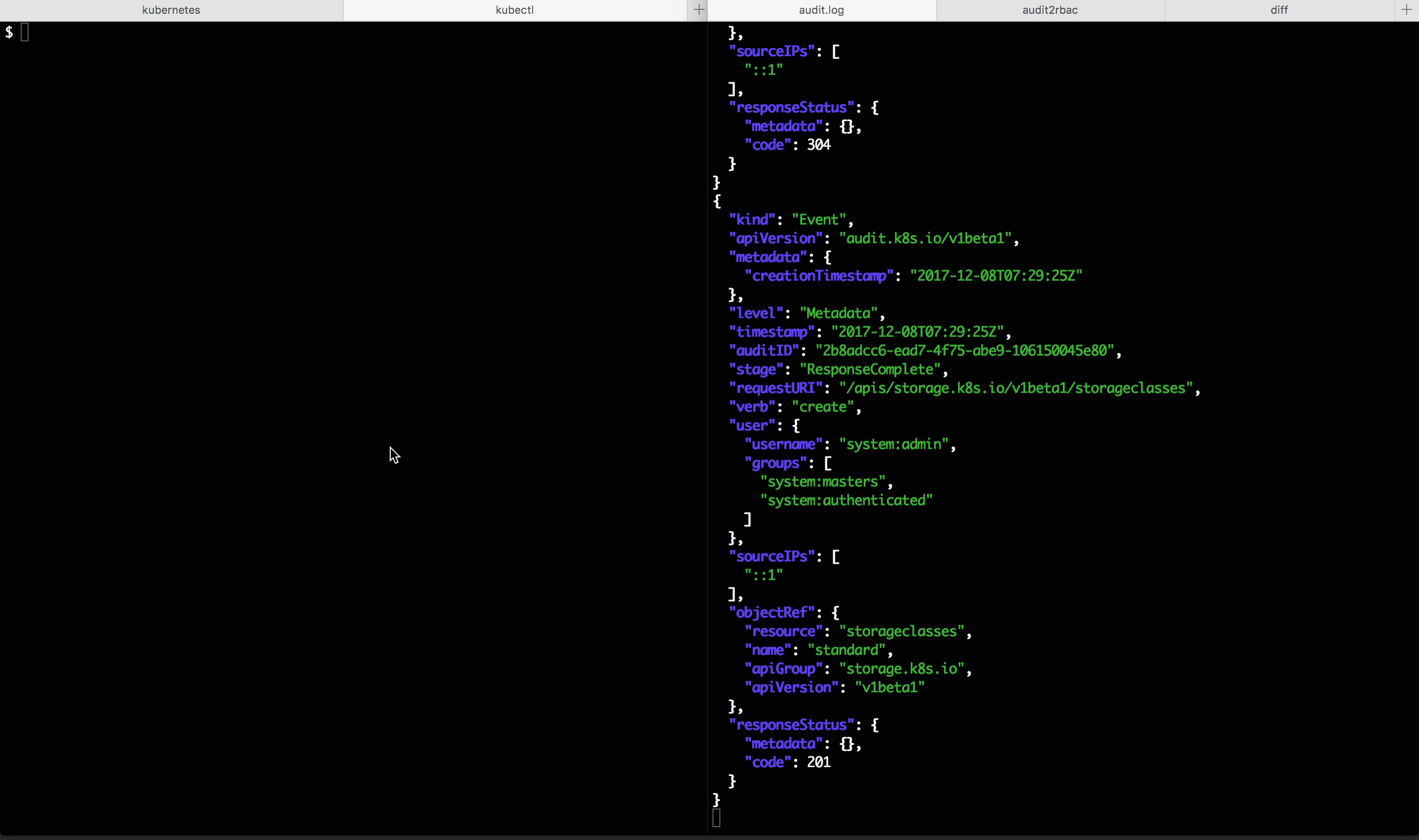
Obtain a Kubernetes audit log containing all the API requests you expect your user to perform:
- The log must be in JSON format. This requires running an API server with
--feature-gates=AdvancedAudit=trueand an--audit-policy-filedefined. See documentation for more details. v1alpha1orv1beta1audit events are supported.- The
Metadatalog level works best to minimize log size. - To exercise all API calls, it is sometimes necessary to grant broad access to a user or application to avoid short-circuiting code paths on failed API requests. This should be done cautiously, ideally in a development environment.
- A sample log containing requests from
alice,bob, and the service accountns1:sa1is available.
- The log must be in JSON format. This requires running an API server with
-
Identify a specific user you want to scan for audit events for and generate roles and role bindings for:
- Specify a normal user with
--user <username> - Specify a service account with
--serviceaccount <namespace>:<name>
- Specify a normal user with
-
Run
audit2rbac, capturing the output:audit2rbac -f https://git.io/v51iG --user alice > alice-roles.yaml audit2rbac -f https://git.io/v51iG --user bob > bob-roles.yaml audit2rbac -f https://git.io/v51iG --serviceaccount ns1:sa1 > sa1-roles.yaml
-
Inspect the output to verify the generated roles/bindings:
more alice-roles.yaml
apiVersion: rbac.authorization.k8s.io/v1 kind: Role metadata: creationTimestamp: null labels: audit2rbac.liggitt.net/generated: "true" audit2rbac.liggitt.net/user: alice name: audit2rbac:alice namespace: ns1 rules: - apiGroups: - "" resources: - configmaps verbs: - get - list - watch - apiGroups: - "" resources: - pods verbs: - get - list - watch - apiGroups: - "" resources: - secrets verbs: - get - list - watch --- apiVersion: rbac.authorization.k8s.io/v1 kind: RoleBinding metadata: creationTimestamp: null labels: audit2rbac.liggitt.net/generated: "true" audit2rbac.liggitt.net/user: alice name: audit2rbac:alice namespace: ns1 roleRef: apiGroup: rbac.authorization.k8s.io kind: Role name: audit2rbac:alice subjects: - apiGroup: rbac.authorization.k8s.io kind: User name: alice
-
Load the generated roles/bindings:
kubectl create -f roles.yaml role "audit2rbac:alice" created rolebinding "audit2rbac:alice" created
Requirements:
- Go 1.8+
- Glide 0.12.3+
To build and install from source:
go get -d github.com/liggitt/audit2rbac
cd $GOPATH/src/github.com/liggitt/audit2rbac
git fetch --tags
make install-deps
make install